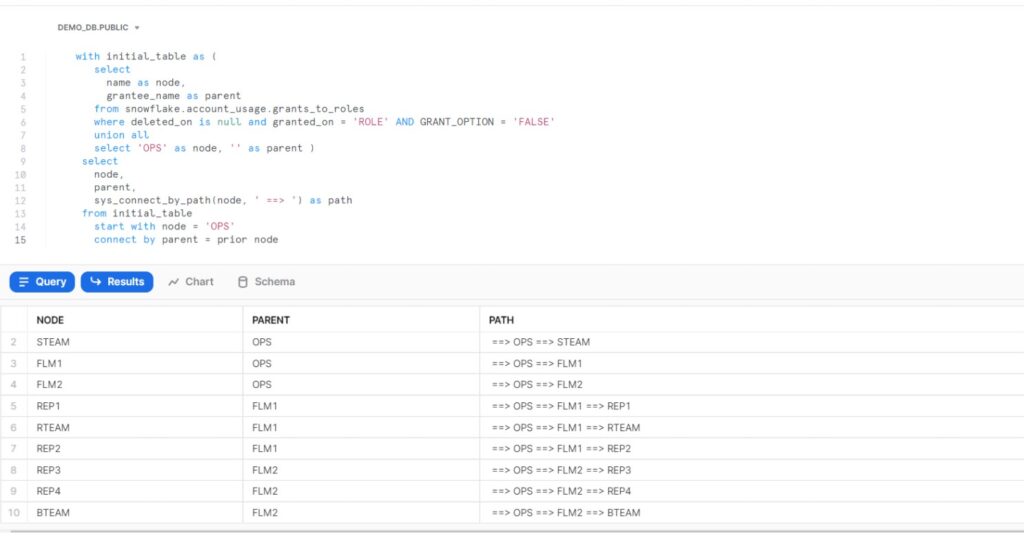
As discussed in previous post ,we have created the Multilevel hierarchy for the Roles. During the implementation of last post we created various Roles i.e. Total number of Roles (10 ) and set up the hierarchy among these Roles. Execute mentioned RBAC Query and it will display Parent-Child relationship.
Role-Based Access Control part of Snowflake’s Access Control Framework , Allows privileges to be granted by Object Owners to Roles. Roles in turn, can be associated with Users to restrict/allow actions to be performed on objects.
The central idea of the Access Control Framework is that every component on a Snowflake database is an Object, And the privileges to these objects rest with Roles. Once object created, RBAC used to access privileges on the Object are assigned to Role(s),In turn assigned to Users.
Roles can be assigned to other Roles which means Role hierarchies are allowed in Snowflake. RBAC enables granular control on objects and also complex access privilege inheritance to accommodate every evolving organizational needs.
Apart from System roles, we have Custom roles created by SECURITYADMIN, However rolled up to SYSADMIN as a manual process
This RBAC Query very handy in case of Real time project where we have ‘N’ numbers of Roles, And defined hierarchy defined among these.
So instead of validating it manually we can leverage the below query and fetch the result in desired hierarchy.
By running this query we can get the 360 degree view of the Roles which are present in the current system.
This will help the developer to grant the required privilege’s to the correct users and avoid the security breach.